A hacked WordPress website is every site owner’s nightmare but the real danger is not knowing it happened. If you suspect your site has been compromised, you are not alone. In fact, a hacked WordPress website rarely announces itself with flashy warning banners. Instead, modern cyberattacks operate in stealth mode, quietly stealing data or hijacking your server resources for months before you notice anything is wrong. Fortunately, knowing exactly what to look for puts you firmly back in control.
Why Hackers Stay Hidden on Purpose
Hackers have largely abandoned “digital graffiti.” Today, they chase stealth monetization. A site that stays online while silently redirecting mobile visitors to an affiliate scam generates far more revenue for attackers than a site they simply destroy.
Moreover, sophisticated malware actively hides from logged-in administrators. As a result, your site looks perfectly normal to you while your visitors encounter a completely different, dangerous version. That gap is exactly where the real damage happens.
Red Flags Inside Your WordPress Dashboard
1. Unknown Admin Users
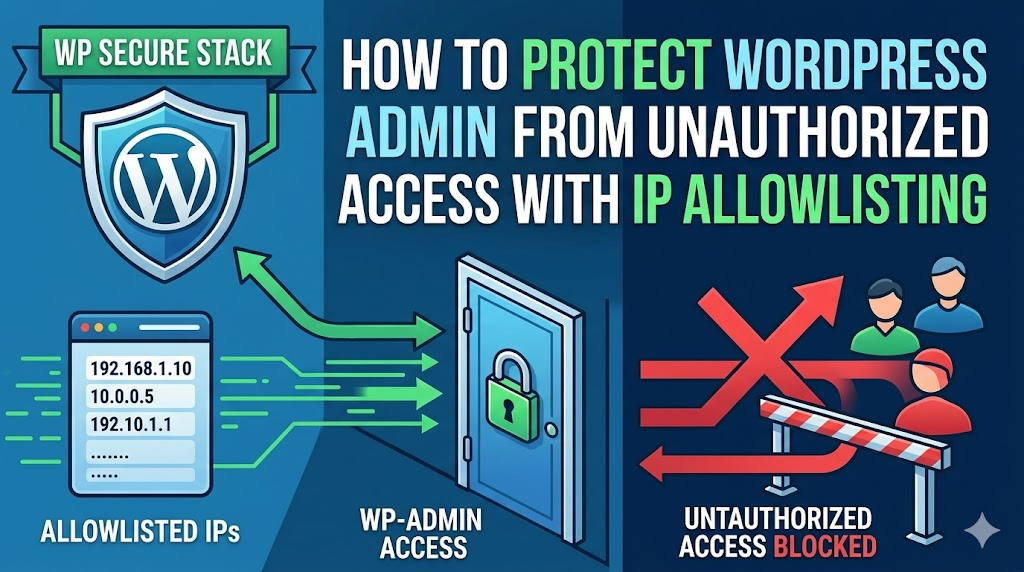
First, head straight to your users list. If you spot a new administrator account with an unfamiliar username or a suspicious email domain, treat it as a confirmed breach until proven otherwise.
2. Unauthorized Plugin or Theme Changes
Next, check your plugins and active theme. Hackers frequently install unauthorized plugins or quietly modify theme files to create “backdoors.” These backdoors let them maintain access even after you change your password.
3. Inability to Log In
If your correct credentials suddenly stop working and password reset emails never arrive, act immediately. A hacker has likely changed your admin email address and locked you out entirely.
4. Sudden Core Update Failures
WordPress core updates normally run without a hitch. Therefore, if updates consistently fail or throw unusual errors, malware is almost certainly blocking the security patches designed to eliminate it.
Red Flags in Search Results and Google Search Console
5. “This Site May Be Hacked” Warning
Google’s automated scanners often catch malware faster than site owners do. If you see this warning appear next to your URL in search results, Google has already detected malicious code on your pages.
6. SEO Spam — The “Japanese Keyword Hack”
Type site:yourdomain.com into Google and scan the results carefully. If you see page titles and descriptions written in foreign languages or advertisements for illegal pharmaceuticals you are actively losing your SEO rankings to an injection attack.
7. Google Search Console Security Alerts
If you have connected your site to Google Search Console, check the Security & Manual Actions report regularly. Google pinpoints specific URLs containing malware or deceptive content, giving you a precise starting point for cleanup.
8. A Sudden Drop in Organic Traffic
Redirects and browser security warnings trigger an immediate, dramatic drop in search traffic. Google rapidly de-indexes pages it identifies as unsafe, so a sharp traffic decline in your analytics is a serious warning sign.
Red Flags in Site Behavior and User Complaints
9. Mysterious Redirects
The “Redirect Hack” is particularly tricky because it often targets only mobile visitors or users arriving from search engines. If users report that clicking your link takes them to a prize page or an adult website, a malicious redirect script is likely hiding in your .htaccess file or site header.
10. The White Screen of Death (WSoD)
A sudden, unexplained white screen can occur when poorly written malware crashes your site’s PHP processing. Although plugin conflicts cause this issue too, a WSoD with no obvious trigger deserves an immediate security scan.
11. A Drastic Performance Slump
Malware frequently hijacks your server’s CPU to send millions of spam emails or mine cryptocurrency in the background. Consequently, if your site suddenly takes 10 or more seconds to load, check your server resource usage before blaming your hosting plan.
12. Strange Content or Pop-ups
Unwanted ads appearing in your sidebars, footers, or as intrusive pop-ups confirm that a malicious script has injected itself into your database or theme files.
Red Flags Inside Your Server Logs
13. Unusual Spikes in Server Resource Usage
Open your hosting dashboard and look at your CPU and RAM usage. If either metric consistently hits 100% with no corresponding traffic spike, a malicious background process is running on your server.
14. Massive Outgoing Email Volume
Hackers love using WordPress sites as spam relays. If your host alerts you about exceeding your email sending limit or if you find thousands of undelivered message notifications — your site is actively sending phishing emails to real people.
15. Frequent Errors in the Error Log
Access your error_log file via FTP or File Manager and look for repeated errors referencing files inside wp-includes or wp-content/uploads. PHP files executing from these folders are a major red flag, since neither folder should run executable code under normal circumstances.
What to Do Right Now If You Spot These Signs
Spotting one or more of these warning signs does not mean all is lost. However, you must act quickly and decisively.
- Call in a professional. If editing code makes you uncomfortable, hire a WordPress security expert to handle full malware removal and site hardening.
- Go offline. Use a maintenance mode plugin or ask your host to restrict site access. This stops further damage to your visitors immediately.
- Create a backup. Back up the current infected state for forensic analysis before you change anything.
- Run a deep scan. Use a reputable security plugin such as Wordfence or Sucuri both offer powerful server-side scanning.
- Change every password. Update credentials for WP-Admin, FTP, your hosting cPanel, and your database without delay.
- Reinstall WordPress core. Replace your
wp-adminandwp-includesfolders with clean copies directly from WordPress.org.
Prevention Always Beats Cleanup
Once your site is clean, enable Two-Factor Authentication (2FA) for all admin accounts and commit to keeping every plugin, theme, and WordPress core installation up to date. Taking these two steps alone eliminates the vast majority of vulnerabilities that lead to a hacked WordPress website in the first place and that is always a far better outcome than scrambling for a cure.


Leave a Reply